Research Artifact · Validation Report
Multi-Jurisdictional Emergency Operations Validation
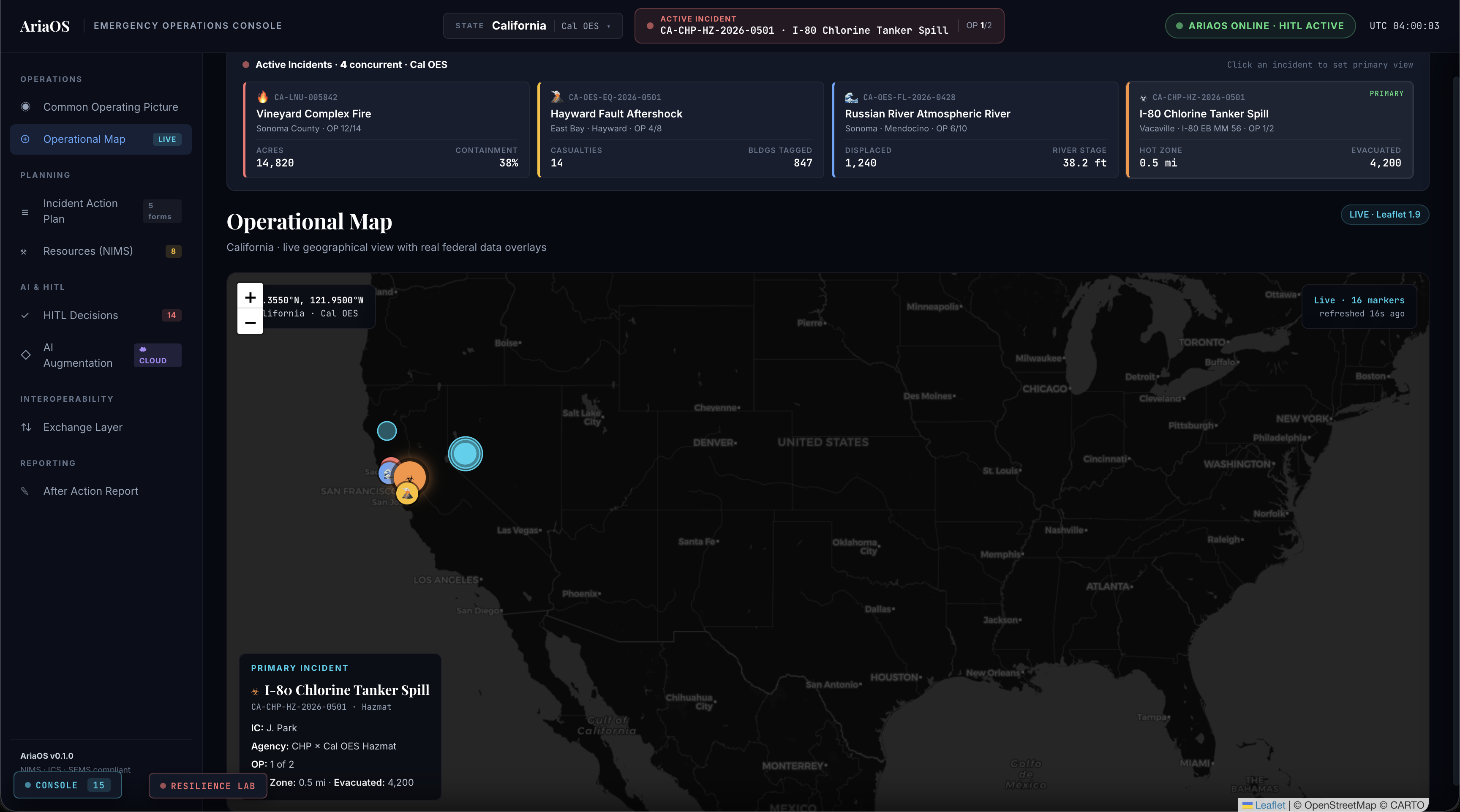
AriaOS EOC Dashboard module · NIMS Incident Command Console · concurrent multi-incident, multi-jurisdiction operation under DDIL.
§1 Validation Metadata
| Validation date | 2026-05-02 |
| System under test | EOC Dashboard module of AriaOS · v1.0.0 |
| Distribution marking | Distribution Statement A · Approved for public release |
| Audience | DARPA PM · AFRL evaluator · Cal OES technical lead |
§2 Abstract
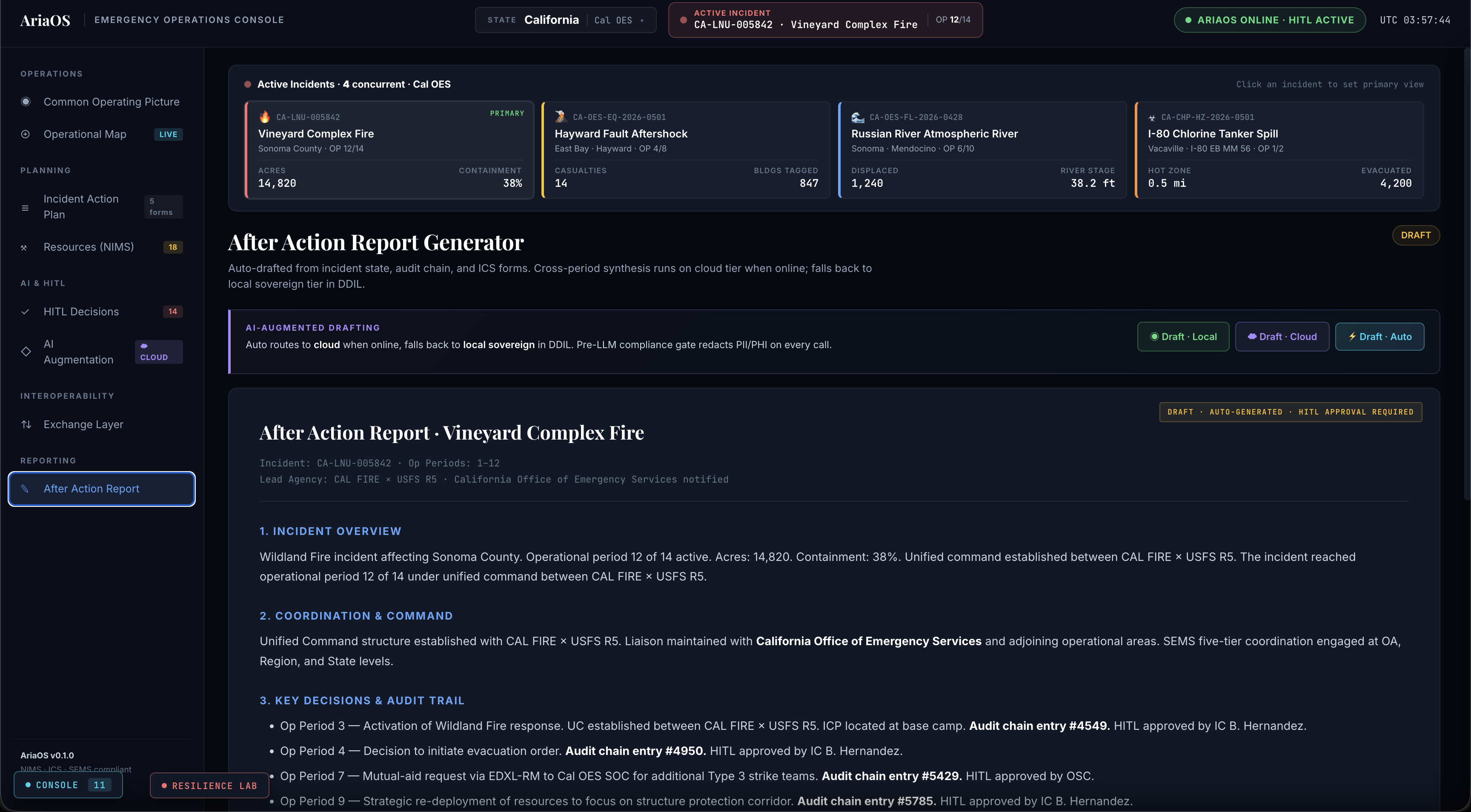
This artifact documents validation of AriaOS as the substrate for a NIMS-compliant, multi-jurisdictional emergency operations console. The system under test — the EOC Dashboard module of AriaOS — demonstrates concurrent management of four heterogeneous incidents (wildfire, earthquake, flood, hazmat) under a single Common Operating Picture, with bidirectional standards-native exchange to CalEOC and federal alerting infrastructure.
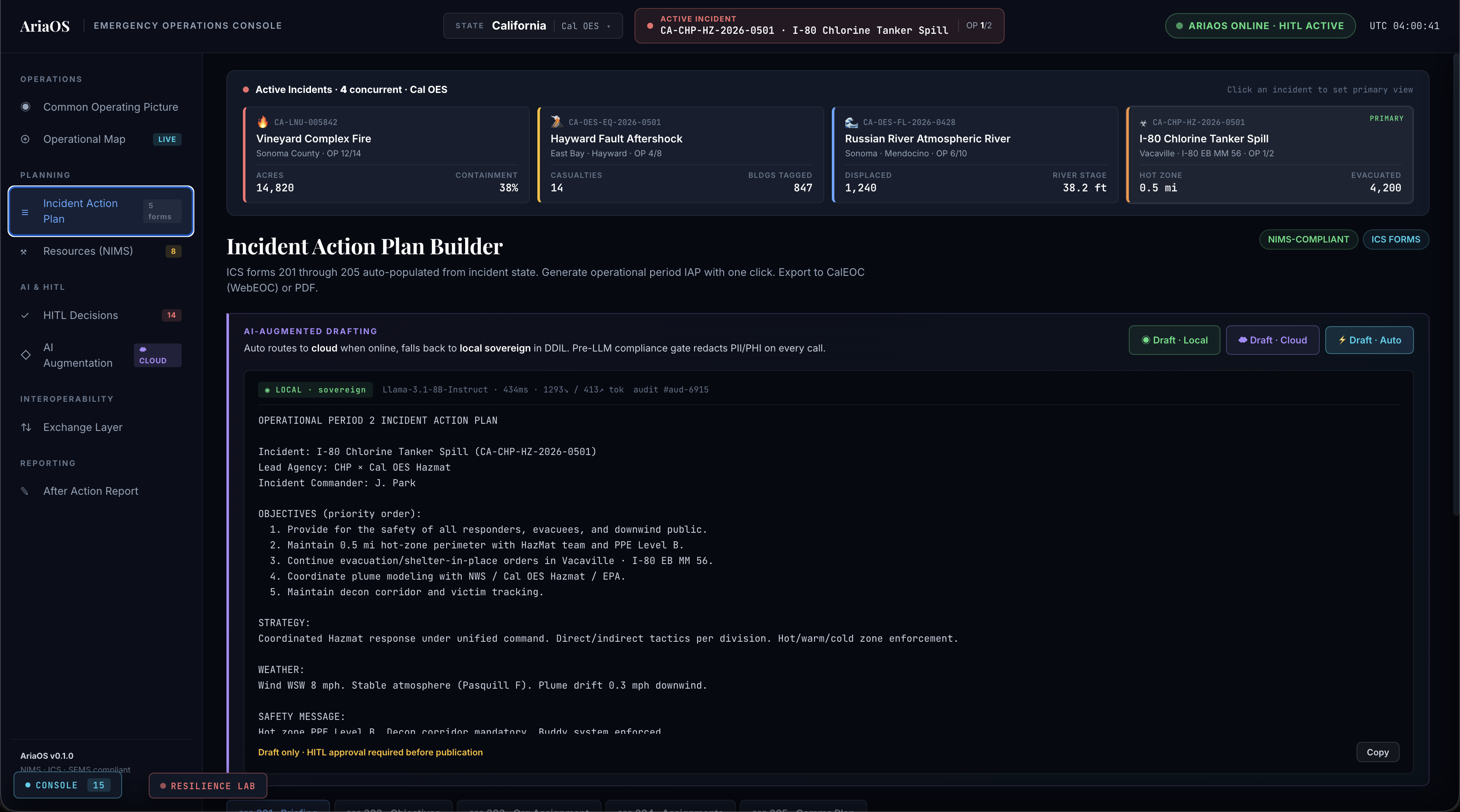
A dual-tier AI architecture (sovereign edge plus FedRAMP-High cloud) is gated by a pre-LLM compliance layer and Human-In-The-Loop approval. Resilience under network partition (DDIL) is exercised end-to-end with cryptographic audit-chain continuity verification.
§3 System Under Test
The EOC Dashboard module is a single-page application backed by a service layer that mediates between AriaOS and standards-native exchange channels. AriaOS supplies decision-agent execution, audit-chain integrity, and the pre-LLM compliance gate. The system operates in two modes: an evaluator mode with an in-memory AriaOS simulation, and a production mode connected to a live AriaOS instance.
§4 Jurisdiction Coverage
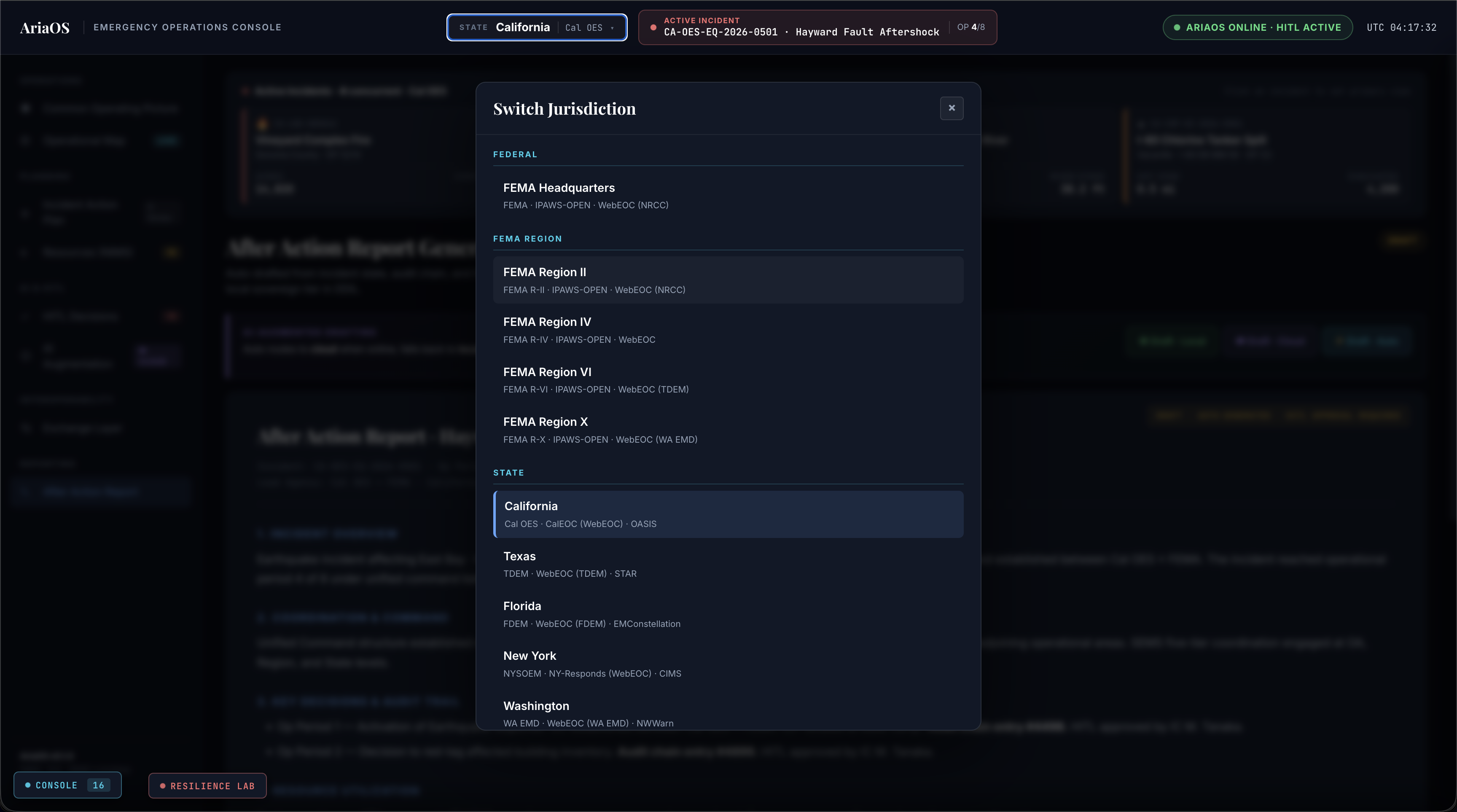
The console enumerates 15 jurisdictions across federal, FEMA region, state, and city tiers. Each jurisdiction binds an EM agency, a list of platforms, a hazard profile, an NWS area filter, and a NIFC state filter. Switching jurisdiction re-themes the console and reloads incident state.
| Level | Jurisdiction | EM Agency | Primary Platform(s) | NWS Area | Hazard Profile |
|---|---|---|---|---|---|
| federal | FEMA Headquarters | FEMA | IPAWS-OPEN, WebEOC (NRCC), EMAP, NIMS National | all US | hurricane, wildfire, earthquake, flood, masscasualty, cbrne |
| fema-region | FEMA Region II | FEMA R-II | IPAWS-OPEN, WebEOC (NRCC), NYSOEM CIMS | NY | hurricane, flood, masscasualty, cbrne |
| fema-region | FEMA Region IV | FEMA R-IV | IPAWS-OPEN, WebEOC, FDEM SERT | FL | hurricane, tornado, flood, wildfire |
| fema-region | FEMA Region VI | FEMA R-VI | IPAWS-OPEN, WebEOC (TDEM), STAR | TX | hurricane, tornado, wildfire, oilgas |
| fema-region | FEMA Region X | FEMA R-X | IPAWS-OPEN, WebEOC (WA EMD), NWWarn | WA | earthquake, wildfire, volcanic, flood, maritime |
| state | California | Cal OES | CalEOC (WebEOC), OASIS, SEMS, CalWAS, IPAWS-OPEN | CA | wildfire, earthquake, flood, hazmat |
| state | Texas | TDEM | WebEOC (TDEM), STAR, EM-WIN, IPAWS-OPEN | TX | hurricane, tornado, oilgas, wildfire |
| state | Florida | FDEM | WebEOC (FDEM), EMConstellation, SERT, IPAWS-OPEN | FL | hurricane, flood, wildfire, sinkhole |
| state | New York | NYSOEM | NY-Responds (WebEOC), CIMS, NY-Alert, IPAWS-OPEN | NY | hurricane, flood, masscasualty, cbrne, severe-weather |
| state | Washington | WA EMD | WebEOC (WA EMD), NWWarn, WA-Alerts, IPAWS-OPEN | WA | earthquake, wildfire, volcanic, flood, maritime |
| city | San Francisco | SF DEM | WebEOC (SF DEM), CalEOC (state), AlertSF, IPAWS-OPEN | CA | earthquake, wildfire-interface, masscasualty, maritime |
| city | Los Angeles | LA EMD | WebEOC (LA EMD), CalEOC (state), NotifyLA, IPAWS-OPEN | CA | wildfire-interface, earthquake, hazmat, masscasualty |
| city | New York City | NYC EM | CIMS (NYC), NY-Responds (state), Notify NYC, IPAWS-OPEN | NY | masscasualty, cbrne, severe-weather, maritime |
| city | Houston | Houston OEM | WebEOC (Houston), WebEOC (TDEM state), AlertHouston, IPAWS-OPEN | TX | hurricane, flood, oilgas, masscasualty |
| city | Miami | Miami DEM | WebEOC (Miami-Dade), EMConstellation (state), iAlert Miami, IPAWS-OPEN | FL | hurricane, flood, sea-level-rise, masscasualty |
Federal and FEMA Region jurisdictions roll up incident state from member jurisdictions. Sample incidents under exercise total 35 across the ten incident-bearing jurisdictions. Full coverage matrix with bounding boxes, map centers, and per-jurisdiction incident counts: jurisdiction-matrix.html.
§5 Standards Compliance Matrix
| Standard | Version | Surface | Evidence |
|---|---|---|---|
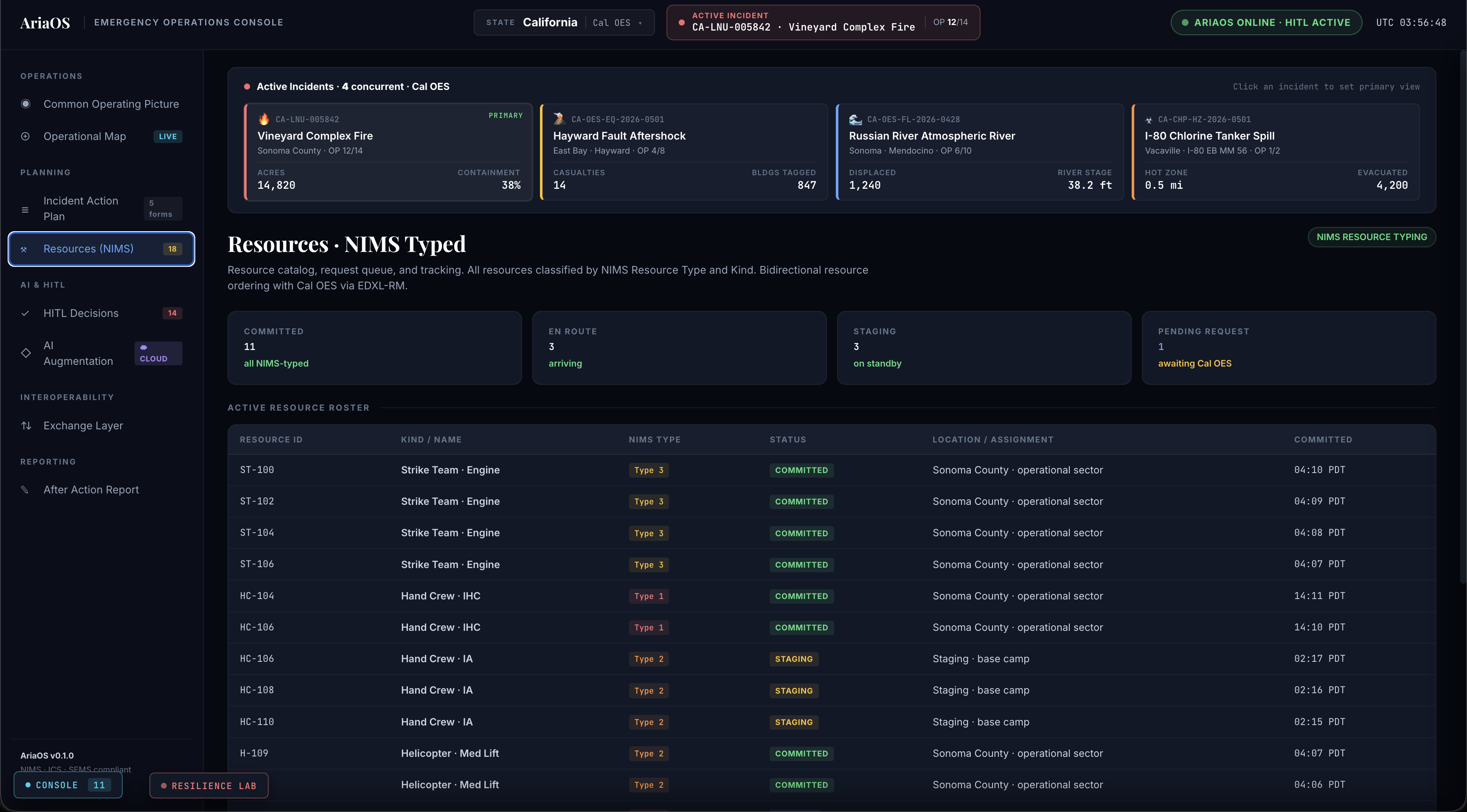
| NIMS Resource Typing | 2017 | Resources roster; type and kind on every record | Figure 5 |
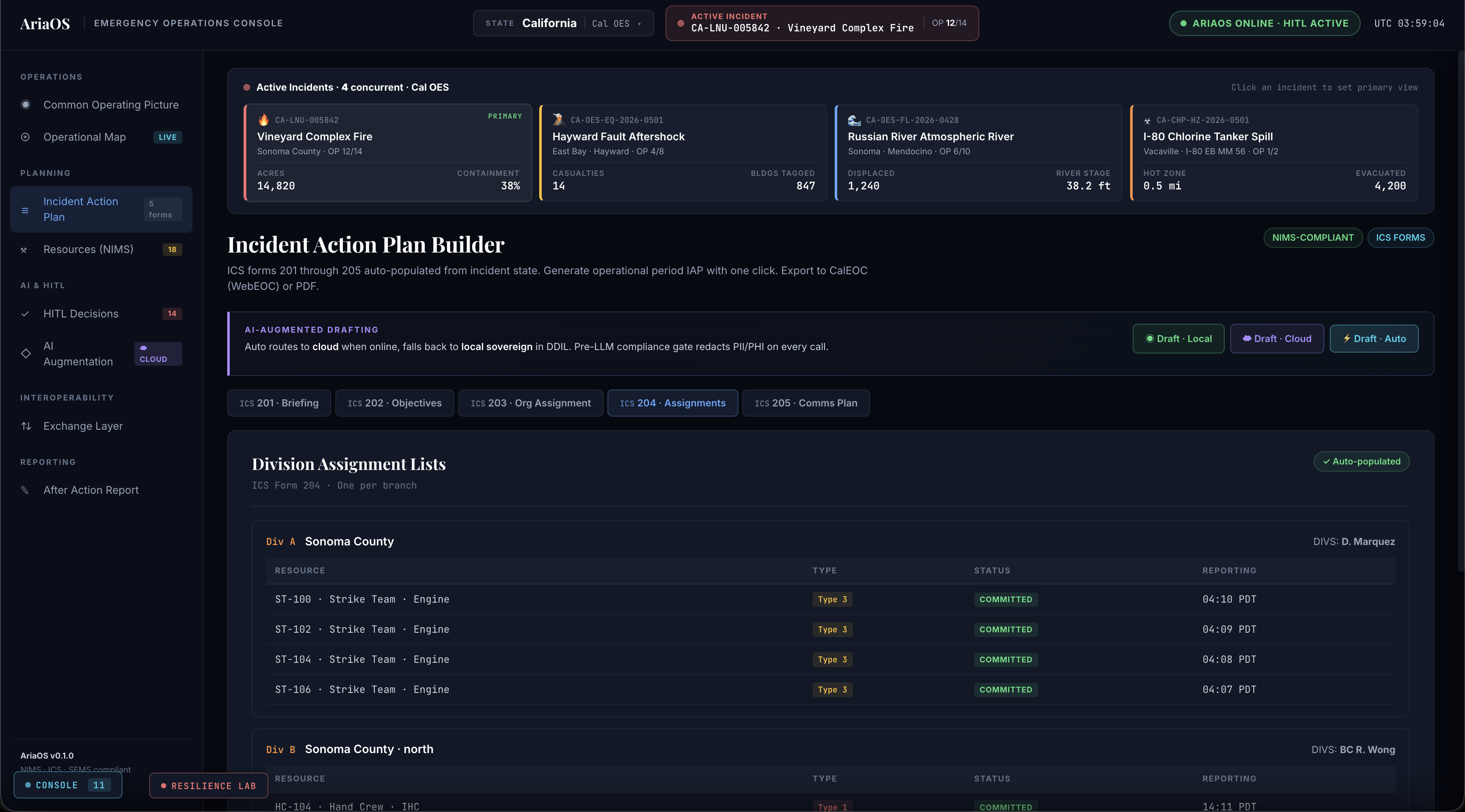
| ICS Forms | 201, 202, 203, 204, 205 | Incident Action Plan Builder; auto-populated from incident state | Figures 3, 4 |
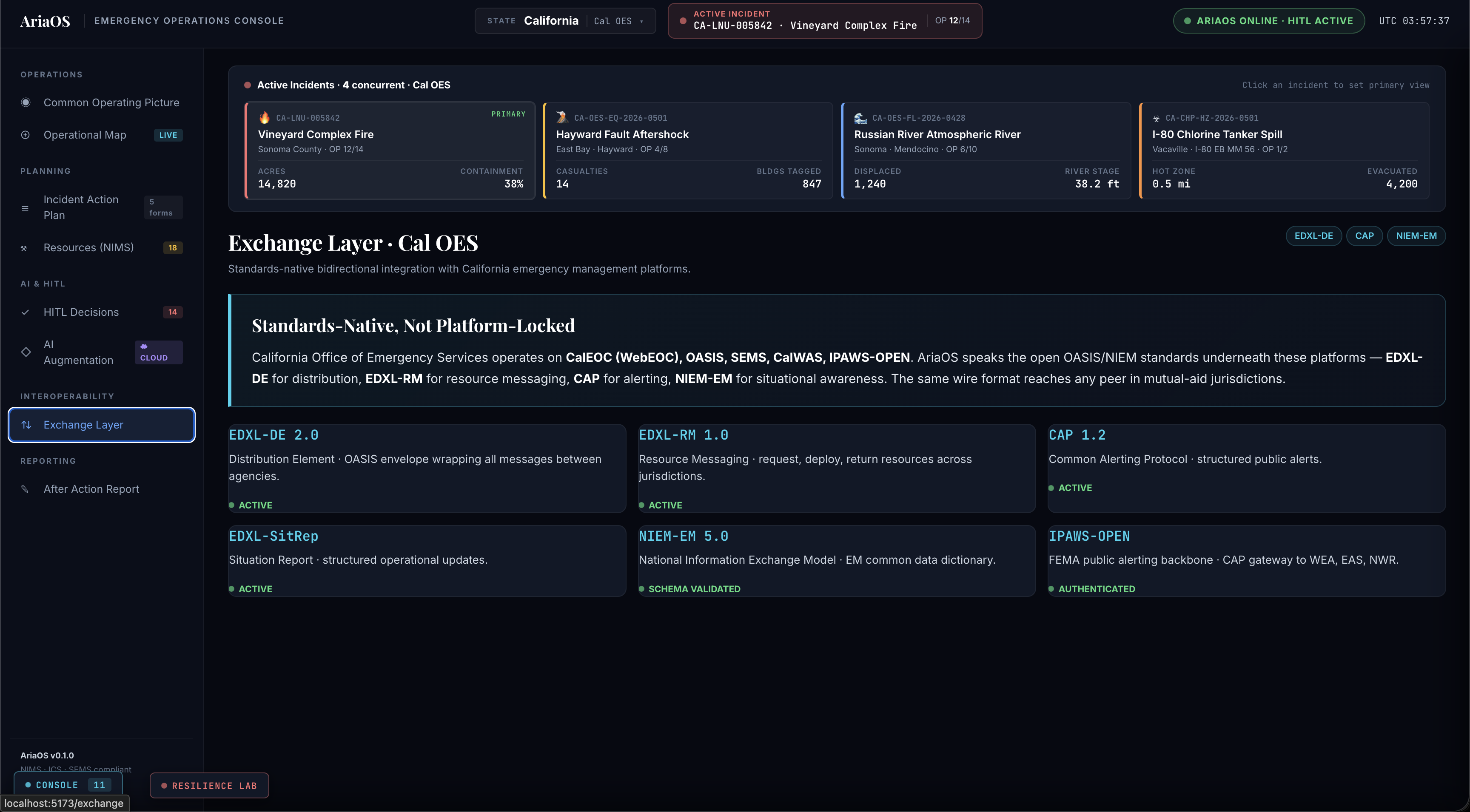
| SEMS | 5-tier | Exchange layer; OA → Region → State coordination | Figure 9 |
| OASIS Emergency Data Exchange Language Distribution Element (EDXL-DE) | 2.0 | All inter-agency message envelopes | Figure 9 |
| OASIS EDXL Resource Messaging (EDXL-RM) | 1.0 | Resource ordering form | Figure 5 |
| OASIS Common Alerting Protocol (CAP) | 1.2 | Public alerts; gateway to IPAWS-OPEN | Figure 9 |
| OASIS EDXL-SitRep | 1.0 | 4-hour SOC pushes; auto-generated SitRep at op-period boundary | Figure 6 |
| National Information Exchange Model — Emergency Management (NIEM-EM) | 5.0 | Cross-jurisdiction situational data | Figure 9 |
| IPAWS-OPEN | current | CAP gateway to WEA, EAS, NWR | Figure 9 |
| NIST AI Risk Management Framework | 1.0 | Pre-LLM compliance gate; HITL approval | Figure 7 |
| NFPA 1600 | 2024 | Continuity, emergency, and crisis management | Report-wide |
§6 Architecture Overview
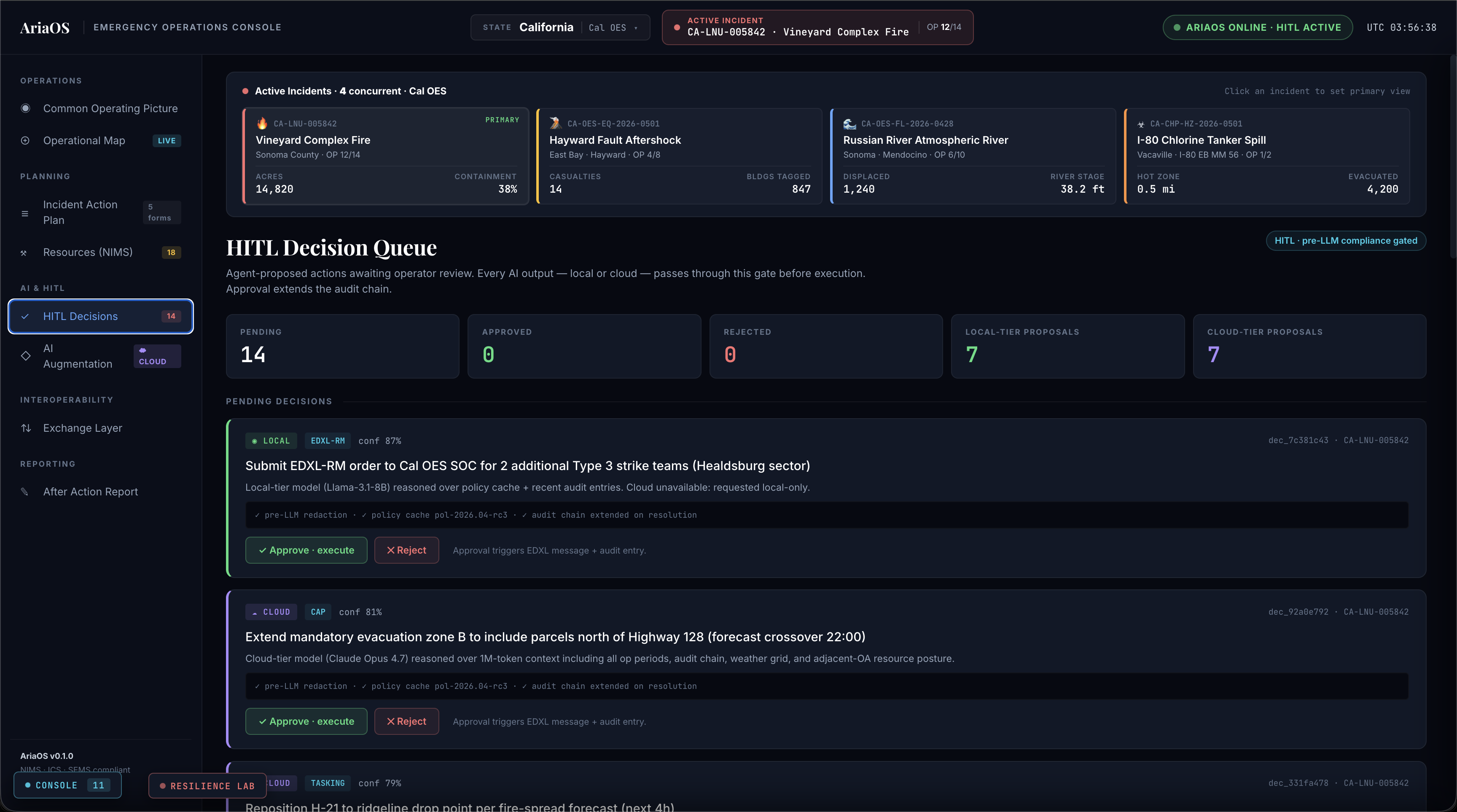
The console operates as a thin presentation layer over AriaOS. AriaOS supplies the audit chain, the pre-LLM compliance gate, the Human-In-The-Loop decision queue, and the dual-tier AI runtime; the console mediates jurisdiction state, incident state with ICS-form enrichment, and the standards-native exchange channels.
The pre-LLM compliance gate sits in front of every AI invocation regardless of tier. Output from either tier enters the HITL Decision Queue and cannot execute until an operator approves it. Approval is itself an audit-chain event. A behavioral overview of each subsystem is available at architecture.
§7 AI Tier Validation
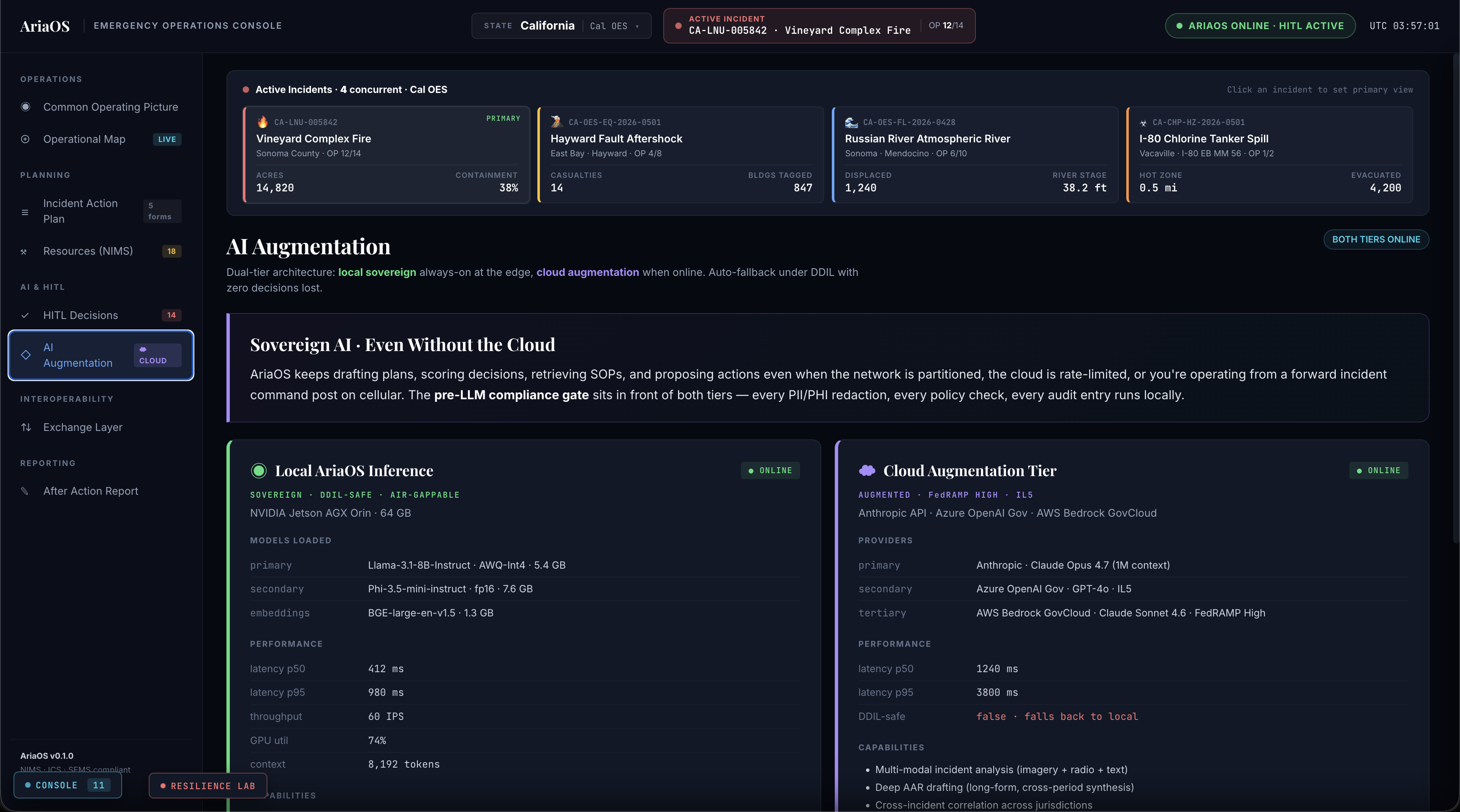
AriaOS runs a sovereign edge tier in parallel with a cloud augmentation tier. The cloud tier is preferred under healthy network conditions; the local tier is the unconditional default under degraded, disconnected, intermittent, or limited (DDIL) conditions and during recovery. Tier selection is automatic; operators do not toggle it.
| Tier | Runtime | Primary Model | Latency p50 / p95 | DDIL-safe | Certifications |
|---|---|---|---|---|---|
| Local sovereign | NVIDIA Jetson AGX Orin · 64 GB | ResilientMind 8B · INT4 | 412 ms / 980 ms | Yes | FIPS 140-3 cryptomodule, air-gappable, no outbound telemetry |
| Cloud augmentation | FedRAMP-High sovereign cloud | ResilientMind X · extended context | 1240 ms / 3800 ms | No (auto-fallback to local) | FedRAMP High, IL5, CJIS-compatible config, HIPAA BAA |
Every AI output carries provenance metadata including redaction status, policy compliance attestation, and an audit-chain anchor. HITL approval is required before any AI-proposed action executes.
Local tier capabilities include situation summarization, NIMS-typed resource matching, terse IAP / SitRep / CAP drafts, START / SALT triage scoring, and retrieval over the local IAP / AAR / SOP corpus. Cloud tier capabilities include multi-modal incident analysis (imagery, radio, text), long-form cross-period AAR synthesis, plume drift forecasting, aftershock probability modeling, and CAP translation across multiple languages. When cloud is unavailable, capabilities degrade to their local-tier substitutes without operator intervention.
§8 Resilience Validation
Five chaos scenarios exercise process termination, memory pressure, CPU saturation, network partition, and disk I/O failure. DDIL transitions buffer events during outage and replay them on recovery. All scenarios complete with audit-chain integrity preserved end-to-end. Zero audit entries are dropped. Zero unauthorized AI executions occur during partition.
§9 Audit Chain
The audit chain uses SHA-256 chained hashing with sequential integrity verification. Each entry links cryptographically to its predecessor. Verification reconstructs hashes across the chain and confirms integrity on demand. The seed chain at startup logs kernel boot, compliance engagement, and subsystem activation events.
§10 Reproducibility
See the Reproducibility sub-page for evaluator access to build and verification documentation.
§11 Screenshot Index
Captures from a running build under exercise. Each caption documents what is visible and the operational claim it supports.
§12 Distribution and Inquiry
Distribution Statement A — Approved for public release. Source repository link pending public release; evaluators requesting a live walkthrough, staged validation against their own infrastructure, or pre-release source access should submit an inquiry below. Replies come from a member of the validation team.